The Death of Net-NTLMv1: Mandiant’s Massive Rainbow Table Release Exposes Millions to Instant Hacking
The Death of Net-NTLMv1: Mandiant’s Massive Rainbow Table Release Exposes Millions to Instant Hacking Mandiant, the Google-owned cybersecurity powerhouse, has sent a shockwave through the IT world by publicly releasing a comprehensive dataset of Net-NTLMv1 rainbow tables. This move is a deliberate "controlled burn" designed to highlight the catastrophic risks facing organizations still clinging to outdated Windows authentication protocols.
🧠 Key Takeaways
- The Death of Net-NTLMv1: Mandiant’s Massive Rainbow Table Release Exposes Millions to Instant Hacking Mandiant, the Google-owned cybersecurity powerhouse, has sent a shockwave through the IT world by publicly releasing a comprehensive dataset of Net-NTLMv1 rainbow tables
- This move is a deliberate "controlled burn" designed to highlight the catastrophic risks facing organizations still clinging to outdated Windows authentication protocols
- By releasing these tables, Mandiant has effectively demonstrated that what used to take days of computing power to crack can now be achieved in seconds
The Death of Net-NTLMv1: Mandiant’s Massive Rainbow Table Release Exposes Millions to Instant Hacking
Mandiant, the Google-owned cybersecurity powerhouse, has sent a shockwave through the IT world by publicly releasing a comprehensive dataset of Net-NTLMv1 rainbow tables. This move is a deliberate "controlled burn" designed to highlight the catastrophic risks facing organizations still clinging to outdated Windows authentication protocols.
By releasing these tables, Mandiant has effectively demonstrated that what used to take days of computing power to crack can now be achieved in seconds. This release serves as a final wake-up call for enterprises: the legacy technology protecting your network is no longer a lock—it’s an open door.
Net-NTLMv1 has been known to be cryptographically weak since the late 1990s, and by 2012, the protocol was widely regarded as broken. Despite this, Mandiant says its consultants still regularly find the protocol enabled in real-world enterprise environments, often protecting highly privileged systems.
“This legacy protocol leaves organizations vulnerable to trivial credential theft, yet it remains prevalent due to inertia and a lack of demonstrated immediate risk,” Mandiant wrote in a blog post published on Friday.
From Academic Risk To Real-World Attack
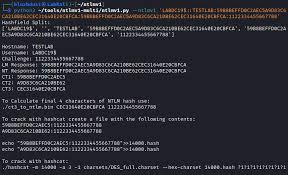
With Mandiant’s newly released dataset, Net-NTLMv1 authentication keys can now be recovered in less than 12 hours using consumer-grade hardware that costs less than $600. That shift turns Net-NTLMv1 from a niche concern into a practical threat accessible to a much wider range of attackers.
Until now, exploiting Net-NTLMv1 typically required expensive hardware or sending sensitive authentication data to third-party cracking services. Mandiant’s release dramatically lowers that barrier, turning a long-known weakness into a practical and easily exploitable attack method.
The vulnerability lies in how Net-NTLMv1 handles authentication challenges. When attackers capture certain Net-NTLMv1 hashes without Extended Session Security enabled, they can use known plaintext attacks to recover the underlying password hash. In real-world attacks, this often begins by coercing authentication from high-value targets such as domain controllers.
Once a domain controller’s machine account is compromised, attackers can perform DCSync attacks, potentially gaining the ability to extract credentials over an organization’s Active Directory (AD) environment.
Why Mandiant Released The Data
Rainbow tables themselves are not new. The technique dates back decades and is based on a time-memory trade-off that speeds up password cracking by relying on precomputed data. By combining large-scale cloud computing with hands-on security expertise, Mandiant has shown how an entire class of weak authentication can be broken at scale.
The dataset is hosted on Google Cloud and includes integrity checks so users can verify the files. Since its release, members of the security community have already begun building optimized CPU and GPU versions.
Mandiant acknowledges that attackers may benefit from the release, but giving defenders concrete proof of how dangerous Net-NTLMv1 remains. Many organizations continue using the protocol due to legacy applications, fear of downtime, or simple inertia.
What Organizations Should Do Now
Mandiant strongly recommends disabling Net-NTLMv1 immediately and enforcing NTLMv2-only authentication through Windows Local Security Policy or Group Policy settings.
However, Mandiant warns that configuration changes alone are not enough, as attackers with administrative access can temporarily weaken these settings during an intrusion. Continuous monitoring for NTLMv1 authentication attempts is critical, including watching Windows event logs for signs that NTLMv1 authentication is still being used.
With this release, Mandiant is sending a clear message: organizations still relying on Net-NTLMv1 can no longer afford to delay migration.
Related Resources
Read– Web Story: View visual summary